I learned a lot playing with UrBackup, but before I conclude it does not meet my particular needs I’d like to absolutely confirm: there is no way to encrypt the transfer from client to server when they are on the same network?
Use internet mode.
Look at Enable internet only mode for details
Thank you, I will try this.
Internet mode works very well.
Hello,
Suggesting using “Internet mode” is like: oh, you don’t want to use unencrypted “telnet” when managing your devices, why don’t you setup your devices you want to manage connecting back to your server over encrypted channel and use reverse shell  Isn’t it?
Isn’t it?
Let’s look into this example:
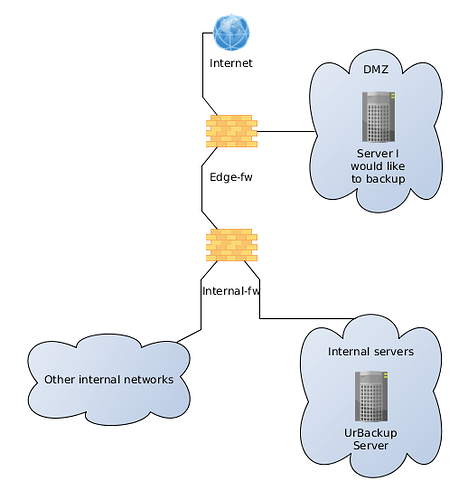
I am a happy UrBackup user backuping all my internal servers/machines using UrBackup and also I would like to start backuping some machines in DMZ… I would like that traffic to be encrypted… In order to do so, I have to allow DMZ host connecting deeper into internal networks to UrBackup server? Does not look OK to me… I would like my UrBackup server connecting to clients and not vice versa…
Agreed, mirkt. UrBackup has some amazing features, but the lack of encryption-by-default is one I can’t comprehend. In virtually any scenario besides a home network I would expect people want their traffic secured from eavesdropping. In my case, a university network full of student laptops running god-knows-what malware, for example. I spent a few hours trying and failing to get internet mode working, so I gave up and plan to check back in on UrBackup in a few years, hoping this great effort continues to evolve.
I don’t think changing the connection direction would make this easier to setup. You didn’t say what your problems were, so that is just a guess…
Also how would one solve the MITM attack problem with the client? There would have to be an UI that shows client fingerprints/or the client fingerprint gets added during setup/creation on the server.
Why not just use TLS (with PFS)… Both client and server should provide a valid certificate (hostname in CN or SAN (Subject Alternative Name)? All “trust issues” could be left to “OS level” - if your machine thinks that certificate is valid (imported into certificate store, provided by own trusted CA and so on…), then it’s ok…
You have a setup where each client in your domain has a valid certificate from your CA? Do you have links on how to do that?
I fully agree that there is no place for unencrypted traffic by default, period.
I don’t know what problems with Internet Mode you encountered, but it works great for me in over a dozen networks and never had any problems with it.
As a bonus it also solves other security related issues caused by default settings so you really should give it another try 
In a Windows network, if you setup a CA, it will generate a valid cert for all your domain-joined systems.